Sharing snapshots on the internet carries significant security risks when sensitive details are accidentally exposed to strangers. Cybercriminals constantly scan public profiles to gather personal data for identity theft and social engineering attacks. Protecting your privacy requires vigilance and an understanding of what constitutes a dangerous upload. Evaluating your digital footprint helps prevent financial loss and physical security threats. The internet never truly forgets what you upload even after you hit the delete button.
Boarding Passes

Travel documents contain a barcode that holds your frequent flyer number and passenger record details. Anyone with a barcode scanner app can easily extract your entire itinerary and personal contact information. Hackers can log into your account to cancel flights or steal thousands of miles in rewards. A simple photo of your departure gate ticket compromises your travel plans entirely. Always shred these slips of paper after you reach your final destination safely.
Passports

Your official travel book contains your exact legal name and date of birth and passport number. Identity thieves covet this combination of data to open fraudulent bank accounts in your name. Forgers can also use these details to create counterfeit documents that enable illegal border crossings. The chip embedded in modern passports holds biometric data that you must protect from unauthorized scanning. Keep this booklet secured in a hidden safe rather than flaunting it for aesthetic travel posts.
Driver Licenses

A new license photograph might seem like a fun milestone to share with friends online. This piece of plastic displays your full home address and signature alongside your physical characteristics. Criminals use this exact information to bypass security questions on your existing financial accounts. Fraudsters can apply for massive loans under your identity using the visible credentials. Securing your driving privileges means keeping this card safely tucked inside your physical wallet.
Credit Cards

Excitement over a new premium rewards card often leads people to make costly uploading mistakes. Even if you cover the main sixteen digits the expiration date and name remain visible. Advanced software can sometimes uncover hidden numbers based on the physical indentation of the plastic. Thieves only need a few visible details to initiate unauthorized purchases on major retail websites. Treat your payment methods with extreme caution to avoid disputing fraudulent charges later.
House Keys

Modern technology allows tech savvy burglars to duplicate a key simply by looking at a clear photograph. Specialized mobile applications can analyze the specific cuts and grooves from a standard image file. Criminals can then use a three dimensional printer or a mail order service to create an exact working replica. This digital duplication process bypasses the need for lock picking tools entirely. Your physical security depends on keeping your key ring hidden from public view.
Work Identification Badges

Celebrating a new job by snapping a picture of your company lanyard creates a major security vulnerability. Corporate badges often feature scannable barcodes and high resolution employee headshots. Malicious actors duplicate these credentials to gain physical access to restricted office buildings. This breach of protocol can result in immediate termination from your new employment position. Securing corporate premises requires keeping all access cards completely offline at all times.
Birth Certificates

Parents sometimes share newborn registration documents to announce an arrival to their extended family. These vital records contain the maiden name of the mother and the exact hospital of birth. These two pieces of information serve as common security questions for almost every major banking institution. Identity brokers sell this pure data on the dark web for hundreds of dollars to sophisticated syndicates. Announce your family additions with cute baby outfits rather than government paperwork.
Mail Envelopes

A photograph of a letter from a famous university or employer might seem harmless at first glance. The front of an envelope displays your complete residential address and full legal name. The postage marks can also indicate exactly which local post office processed the delivery. Stalkers use this precise geographic data to monitor your daily movements and physical whereabouts. Crop out all packaging labels before sharing your exciting acceptance letters with the world.
Car License Plates

Showing off a newly purchased vehicle is a proud moment that requires careful image cropping. A visible license plate allows anyone with access to public records to find your home address. Private investigators and debt collectors frequently use this public registry to track individuals across state lines. The data reveals the exact make and model of your car along with your registration history. Obscure the metal tags with a digital blur before uploading pictures of your new ride.
Bank Statements
Achieving a savings goal might tempt you to post a screenshot of your online banking dashboard. These financial records reveal your account numbers and exact institutional routing codes. Fraudsters use this exact combination to authorize electronic wire transfers out of your checking account. The visible transaction history also exposes your daily spending habits and favorite local stores. Financial milestones should remain a private celebration rather than public internet knowledge.
Tax Documents
Tax season often prompts frustrated citizens to share pictures of their complicated filing paperwork. These federal forms contain your Social Security number and total annual household income. Criminals file fraudulent return claims early in the year using these exact stolen credentials. The government might then delay your legitimate refund check by several months while investigating the fraud. Keep your financial reporting forms securely stored in a locked filing cabinet at home.
Vaccination Cards

Public health records contain specific medical lot numbers and dates of clinical administration. Counterfeiters scour the internet for these authentic details to produce convincing fake medical documents. Your full name and date of birth printed at the top add another layer of identity theft risk. Medical privacy laws exist specifically to keep your personal healthcare decisions entirely confidential. Store these important clinical records alongside your passport rather than displaying them online.
Prescription Medicine Bottles

Sharing your recovery journey online should never include clear shots of your pharmacy labels. The orange bottles display your prescribing doctor and your specific medication dosage. Insurance scammers use this information to call in fraudulent refills under your established patient profile. The label also contains a unique prescription number that grants access to your broader medical history. Peel the stickers off your empty bottles before throwing them into the recycling bin.
Medical Bills

Outrage over healthcare costs frequently leads patients to upload photographs of massive hospital invoices. These billing statements contain your patient identification number and specific diagnostic codes. Fraudsters can utilize these identifiers to submit fake claims to your health insurance provider. This medical identity theft can permanently alter your health records with incorrect blood types or allergies. Express your frustration about medical expenses without exposing the detailed paper invoices.
Childrens School Uniforms

Back to school pictures featuring recognizable school logos place young students at physical risk. Predators use these crests to identify exactly where a child spends their weekdays. The specific uniform colors and patterns make it incredibly easy to pinpoint the exact educational district. Strangers can use this knowledge to approach a child claiming to know their teachers. Photograph your children in neutral clothing if you plan to share the images on public platforms.
Childrens Report Cards
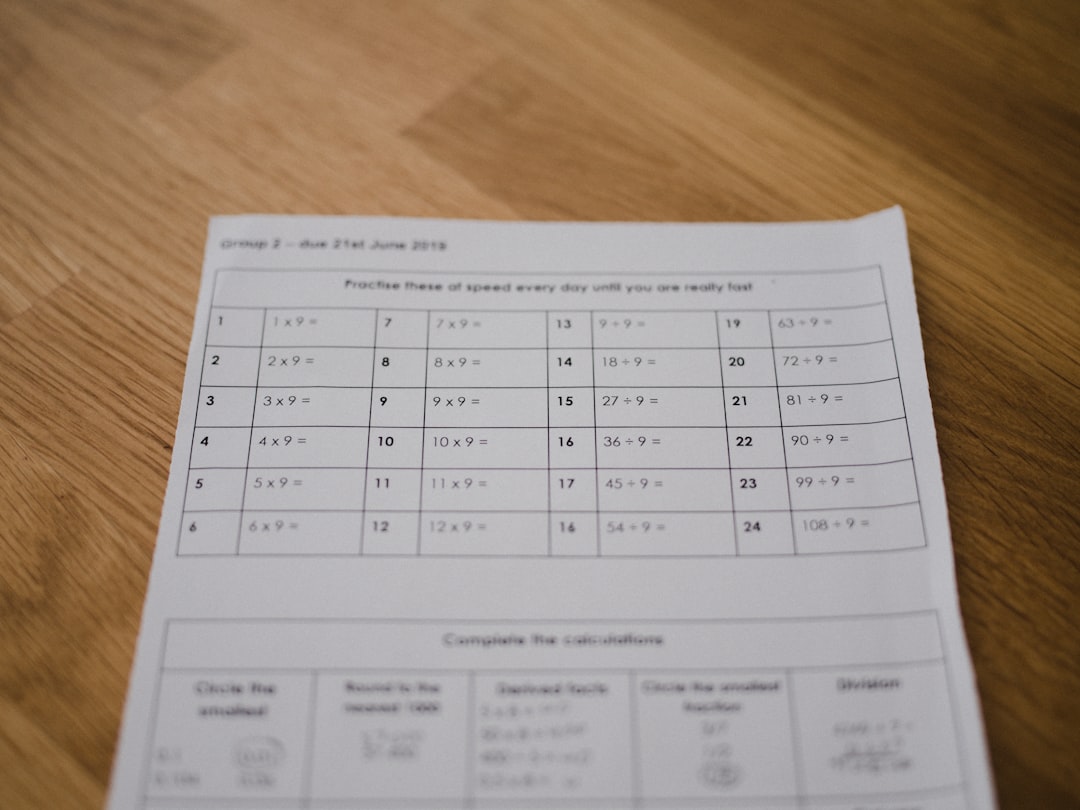
Proud parents love highlighting academic achievements by posting term grades on social networks. These official school documents print the student identification number and full classroom assignment. Bad actors can use this data to impersonate a parent when calling the school administration office. The academic marks themselves can also subject the child to unwanted public scrutiny and teasing. Celebrate a perfect grade point average with a special dinner instead of a digital broadcast.
Home Layout Floor Plans

Building a custom house brings immense joy that owners want to share during the construction process. Detailed architectural blueprints reveal every entrance and window location to potential intruders. Burglars study these schematics to identify blind spots and determine the fastest escape routes. The plans also indicate where you plan to install your master bedroom safe and security panels. Keep the architectural drawings strictly between your family and your hired contractors.
Computer Screens With Tabs Open

A casual picture of your messy desk might inadvertently capture your active computer monitor. Browser tabs often display the titles of confidential internal work documents or personal banking portals. A quick zoom on the image can reveal sensitive email drafts or private chat messages in the background. Cybercriminals hunt for these accidental disclosures to gather intelligence for targeted phishing campaigns. Always minimize your active windows before taking a photograph of your home office setup.
Blank Checks
Receiving a new batch of customized checks might prompt a poorly considered aesthetic photograph. The bottom of every check prints your routing number and personal account number in clear text. Thieves can print their own counterfeit checks using those exact magnetic ink character recognition numbers. This type of financial fraud can drain your checking balance to zero dollars in a matter of hours. Keep your paper checkbooks locked away and never expose them to a camera lens.
Ultrasound Photos With Patient Information

Expectant parents naturally want to share their initial sonogram images with the entire world. The border of the medical monitor usually displays the full legal name of the mother and the clinical facility. Medical identification numbers are often printed directly above the actual baby image. This compromises patient privacy and provides scammers with pristine data for targeted maternal product scams. Crop the image tightly around the actual sonogram to protect your sensitive healthcare details.
Legal Contracts
Signing a lease or finalizing a business deal represents a major milestone worth celebrating. Photographing the actual contract pages exposes confidential binding terms and financial obligations. Competitors can exploit this proprietary business information to undercut your future negotiations. The signatures on the final page give forgers a perfect template to copy your exact handwriting style. Use a generic pen and blank paper for your celebratory signing photos instead.
Security System Panels

Showing off a new smart home setup often includes a shot of the wall mounted security keypad. The brand name alone tells experienced burglars exactly which exploit techniques to use. The photograph might capture the master code if the buttons show distinctive wear patterns. Some panels display the current network status and highlight which specific zones remain unarmed. Maintain your physical safety by keeping all alarm system hardware off your digital feeds.
Wireless Network Passwords

Creating a cute chalkboard sign with your guest internet credentials seems like great hospitality. Posting this sign online allows unauthorized users to access your local area network from nearby. Hackers parked outside can join your network to intercept unencrypted traffic and steal digital passwords. They can also use your internet connection to conduct illegal activities that trace back to your physical address. Share your connection details only verbally with trusted friends who enter your home.
High Value Jewelry Photographs

Flaunting an expensive engagement ring or a luxury watch attracts the wrong kind of digital attention. High resolution macro photographs allow skilled jewelers to identify the exact cut and clarity of the stones. Thieves use these images to assess the retail value of the items before planning a targeted residential burglary. Insurance companies might also deny claims if they determine you recklessly advertised the valuables online. Keep the focus on the emotional moment rather than the microscopic details of the diamonds.
Winning Lottery Tickets

The sheer thrill of a massive jackpot causes many winners to post their lucky numbers instantly. The unique barcode on the ticket serves as the only proof of purchase required to claim the cash. Scammers can use a clean photograph of this barcode to claim your prize electronically before you reach the local office. State lottery commissions strictly enforce a rule that whoever scans the code first receives the payout. Secure your winning ticket in a safe place until you can officially present it in person.
Package Tracking Numbers

Expecting a highly anticipated delivery makes people eager to share their shipping status screens. The long alphanumeric tracking code provides access to the entire logistical journey of the cardboard box. Malicious actors can call the shipping company to reroute the package to a completely different state. The tracking portal also reveals the exact dimensions and weight of the inbound commercial merchandise. Blur out the entire tracking string when complaining about delayed transit times online.
Court Documents

Legal proceedings generate massive amounts of paperwork that citizens sometimes upload out of anger. Subpoenas and civil complaints contain highly sensitive allegations and unredacted personal identifiers. Broadcasting these documents can violate strict judicial gag orders or protective sealing mandates. This digital recklessness can result in severe financial contempt charges or a completely dismissed lawsuit. Consult a qualified legal professional before making any judicial paperwork public on the internet.
Confidential Work Projects

Employees proud of a major presentation sometimes photograph their desk littered with proprietary notes. These whiteboards and printed spreadsheets contain unreleased product features and internal revenue projections. Rival companies eagerly monitor social platforms to steal upcoming strategic business plans. Human resource departments actively monitor the internet to terminate staff members who violate nondisclosure agreements. Keep all corporate materials strictly within the secure confines of the office environment.
Personal Phone Numbers
Adding your mobile digits to a public profile seems like a great way to stay connected with peers. Automated scraping bots harvest these unprotected numbers to sell to aggressive telemarketing agencies. Hackers can execute targeted spoofing attacks to bypass two factor authentication on your critical email accounts. Constant spam messages and malicious phishing texts will quickly render the device completely unusable. Utilize dedicated messaging applications to communicate rather than broadcasting your direct cellular line.
Location Tagged Current Hangouts

Checking into a local coffee shop or restaurant alerts the entire internet to your exact physical location. This real time broadcast informs potential burglars that your residential property currently sits completely empty. Stalkers can easily navigate to the business to initiate an unwanted physical confrontation. The digital breadcrumbs create a highly predictable pattern of your weekly recreational routines. Post your gorgeous food pictures only after you have safely returned to your house.
Please share your thoughts on these digital privacy tips in the comments.