Cybercriminals have become extraordinarily skilled at disguising malicious intent behind messages that look completely routine and trustworthy. Modern phishing attacks no longer rely on broken English or obvious red flags but instead mimic the exact tone and format of legitimate communications from brands and institutions people interact with daily. Understanding which message types are most commonly weaponized can make the difference between staying safe and handing over sensitive credentials. The following examples represent the most deceptive and widely used phishing formats targeting everyday users right now.
Package Delivery Notification

A message arrives claiming a parcel could not be delivered and that a small redelivery fee must be paid to release it. The text typically includes a convincing tracking number and the branding of a well-known courier service. A short link directs the recipient to a near-perfect replica of an official delivery website asking for card details. These scams surge dramatically during peak shopping seasons when people are genuinely expecting deliveries.
Bank Security Alert

An urgent message appears to come directly from a major bank warning that suspicious activity has been detected on the account. The recipient is told to verify their identity immediately by clicking a link or risk having their account suspended. The linked page replicates the bank’s official login portal down to the correct logo placement and color palette. Victims who enter their credentials hand over full account access to attackers within seconds.
Apple ID Suspension

A professionally formatted email warns that the recipient’s Apple ID has been locked due to an unrecognized sign-in attempt from a foreign device. The message lists a specific country and device type to create a strong sense of authenticity and personal relevance. A button labeled “Verify Now” leads to a cloned Apple login page designed to harvest both the password and two-factor authentication codes. Apple users are frequent targets because their accounts are often linked to payment methods and personal data.
Netflix Password Reset

An email informs the recipient that their Netflix password was recently changed and asks them to confirm the action or secure the account immediately. The formatting closely mirrors genuine Netflix communications including the familiar red and black color scheme. The embedded link leads to a fraudulent page that captures login credentials before redirecting users to the real Netflix website. This scam exploits the widespread use of the platform to maximize the pool of potential victims.
PayPal Transaction Alert

A message appears to confirm a large outgoing PayPal payment the recipient did not authorize, creating immediate alarm and urgency. The email instructs the user to click a link and log in to dispute the transaction before it is processed. The fraudulent login page captures the email address and password while the promised transaction dispute feature leads nowhere. PayPal scams are particularly effective because financial urgency prompts people to act before they think critically.
Google Account Warning

An official-looking email from what appears to be Google states that the account has been accessed from an unrecognized location. The message includes a map image or location name to heighten believability and personal concern. The recipient is directed to review account activity through a link that leads to a fake Google sign-in page. Because Google accounts are central to so many digital services the threat of losing access feels especially catastrophic.
IRS Tax Refund
A message claims the recipient is owed a tax refund and must submit their banking information to receive the deposit promptly. The communication uses official-sounding language and may include a fake case number or reference code. A form on the linked page requests bank account details Social Security numbers and home addresses under the guise of identity verification. Tax season creates a reliable window of opportunity for scammers running this format at scale.
NHS Appointment Confirmation

A text message arrives appearing to come from a national health service confirming a medical appointment and requesting confirmation of personal details. The link embedded in the message leads to a page mimicking an official health portal and asking for date of birth and address. In some versions the victim is asked to pay a nominal administrative fee which is used to capture card information. Healthcare-themed phishing is particularly effective because recipients rarely question messages tied to medical matters.
Amazon Order Confirmation

An email mimics an Amazon order confirmation for a high-value item the recipient never purchased, triggering immediate concern. The message includes a fake order number and a prompt to cancel the order through a provided link if the purchase was not authorized. The cancellation page is a replica of Amazon’s website and captures account login details during the fake cancellation process. Amazon’s enormous user base makes this one of the most scalable phishing formats in circulation.
Microsoft License Renewal

An email warns that a Microsoft 365 subscription or software license is about to expire and that service will be interrupted if payment is not updated. The message uses Microsoft’s official fonts and formatting to appear indistinguishable from genuine renewal reminders. A link directs the recipient to a payment page requesting credit card details and billing information. Businesses are frequently targeted with this format because uninterrupted software access feels non-negotiable to working professionals.
Lottery Win Notification

A message informs the recipient that they have won a significant cash prize or gift voucher through a draw they allegedly entered. The email asks for personal details and sometimes a small processing fee before the prize can be released. No legitimate lottery or prize draw requires a payment from the winner as a condition of receiving the reward. This format persists because it taps into the universal appeal of unexpected financial gain.
LinkedIn Connection Request

A message appears to arrive from LinkedIn notifying the recipient of a pending connection request from a professional in their industry. The email urges the user to log in and review the request through an embedded button. The linked page captures LinkedIn credentials on a page designed to match LinkedIn’s interface exactly. Professional networks are valuable targets because accounts often contain personal work history salary details and private messages.
Subscription Cancellation Confirmation

An email confirms the cancellation of a subscription the recipient never actually requested, prompting an urgent desire to reverse the action. A prominent button labeled “Undo Cancellation” leads to a fraudulent login page capturing account credentials. The scam works by exploiting the fear of losing a service the user values and actively uses. Streaming services software tools and cloud storage platforms are the most commonly impersonated services in this format.
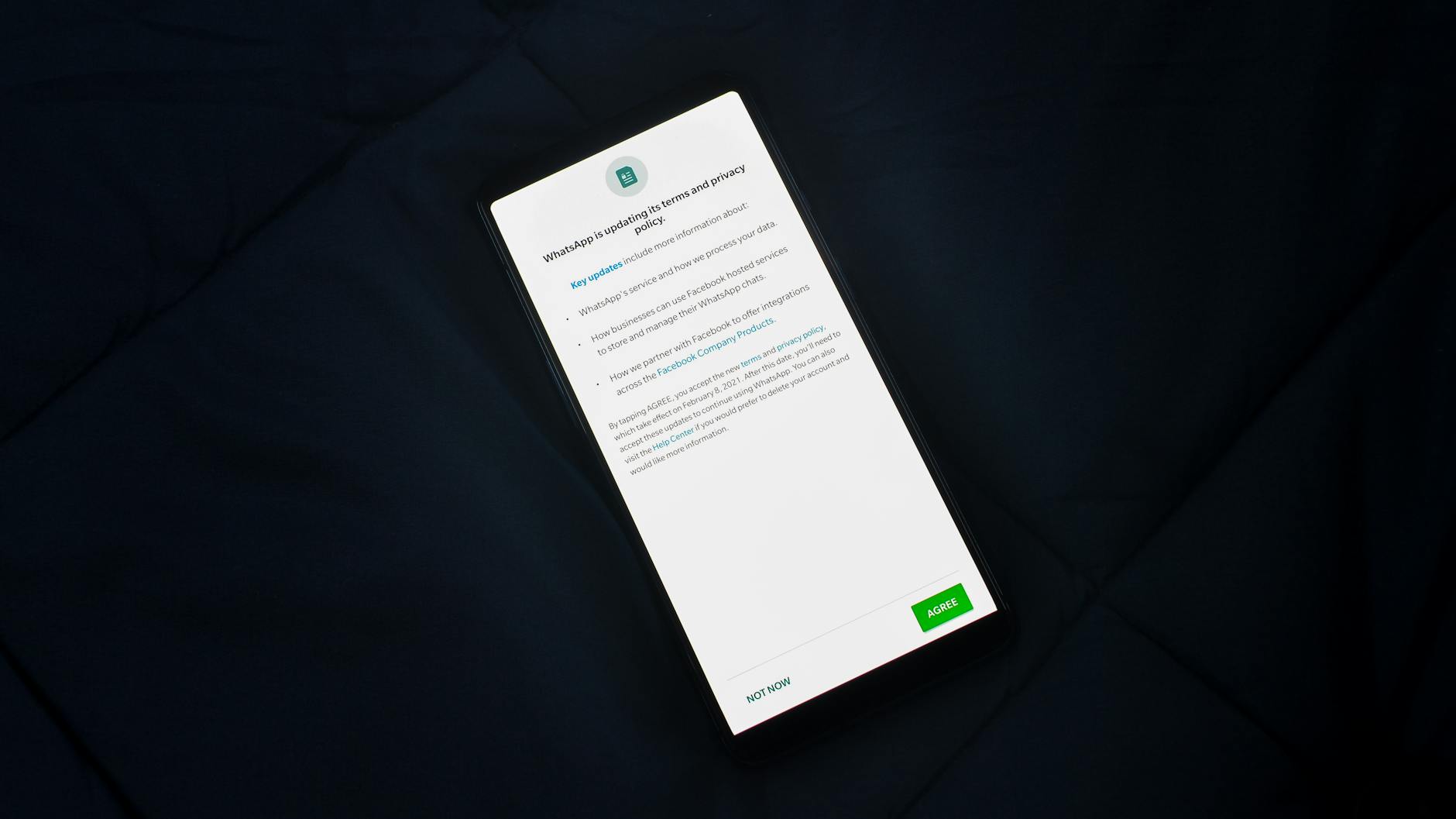
Two-Factor Authentication Request
A message claims that a two-factor authentication code is needed to verify an account login on a new device. The recipient is asked to enter the code on a linked page or reply directly to the message with the digits. Sharing a two-factor code in this way bypasses what is widely considered the most reliable layer of account security. Sophisticated real-time phishing operations can use the submitted code to log into the real account within the few seconds it remains valid.
Charity Donation Receipt

An email arrives that appears to be a receipt for a charitable donation the recipient did not make, designed to provoke a response. The message includes a link to “dispute the charge” which leads to a page collecting card details under the guise of a refund process. Charity-themed scams often spike following natural disasters or public crises when donation activity is at its highest. The use of a sympathetic cause adds an extra layer of perceived legitimacy to the fraudulent communication.
Airline Ticket Confirmation

A message confirms a flight booking for a journey the recipient never arranged, including realistic-looking flight details and a booking reference. A link to “manage or cancel” the booking leads to a page that harvests personal and payment information. The level of detail included in these messages makes them difficult to distinguish from genuine airline communications. Frequent flyers and those who have recently searched for travel are disproportionately targeted by this format.
Utility Bill Overdue Notice
A message claims the recipient’s electricity gas or water account has an overdue balance that must be paid immediately to avoid service disconnection. A link leads to a fraudulent payment portal that captures card details. The threat of losing access to essential utilities creates a powerful emotional response that overrides critical thinking. Scammers tailor these messages by geography so recipients receive notices from providers that are actually active in their region.
HR Policy Update

An internal-looking email purportedly from a company’s human resources department instructs employees to review and acknowledge an updated workplace policy. A link directs the recipient to a fake company login page to “authenticate” before accessing the document. Employees rarely question communications that appear to come from within their own organization especially when they carry the tone of a formal internal directive. This format is a common entry point for corporate credential harvesting and subsequent data breaches.
Pharmacy Prescription Ready
A text message claims a prescription is ready for collection at a local pharmacy and asks the recipient to confirm personal details before pickup. The link leads to a page requesting date of birth insurance details or payment card information. Medical urgency and the trusted nature of healthcare providers make recipients far less likely to scrutinize the message carefully. These scams have grown more targeted as fraudsters incorporate details about specific regional pharmacy chains to add authenticity.
Wi-Fi Network Login

A login page appears on a device when connecting to a public Wi-Fi network at an airport hotel or cafe claiming credentials are needed to access the internet. The page may ask for an email address and password combination that the user also uses on other platforms. Unlike email-based phishing this method captures credentials passively without requiring the victim to click a suspicious link in a message. Travelers and remote workers who rely heavily on public internet connections are most frequently exposed to this format.
Zoom Meeting Invitation

An email arrives appearing to be a Zoom meeting invitation from a colleague manager or known contact with a familiar subject line and meeting details. The link to “Join Meeting” leads to a fraudulent Zoom login page that captures email addresses and passwords. Remote and hybrid workers who attend multiple video calls daily are especially vulnerable because these invitations are entirely routine. This scam format became significantly more prevalent as video conferencing became a standard part of professional life.
Student Loan Relief
A message claims the recipient qualifies for a government student loan forgiveness program and must apply immediately before a deadline passes. A form on the linked page collects Social Security numbers income details and banking information under the appearance of an official application. These scams increase in frequency during periods of genuine government debate around student debt policy. Young adults managing loan repayments are the primary demographic targeted by this format.
Parental Consent Form
An email appearing to come from a school or educational institution asks a parent to complete an urgent consent form for an upcoming activity or policy change. The link leads to a page requesting login credentials or personal identification details to access the form. Schools and educational bodies are trusted institutions and communications from them are rarely questioned by recipients. Scammers exploit the start of academic terms and periods of policy change to make timing feel plausible.
Social Media Copyright Warning

A message warns that a post or image shared on a social media account has been flagged for copyright infringement and that the account will be suspended if no action is taken. A link leads to a login page mimicking the platform’s interface where credentials are captured. The fear of losing a valued social media account prompts immediate action without proper scrutiny of the message’s legitimacy. Creators and businesses that depend on social platforms for income are particularly susceptible to this format.
Crypto Wallet Verification

A message claims that a cryptocurrency wallet or exchange account requires immediate identity verification to comply with new regulatory requirements. The recipient is directed to a page requesting government ID uploads wallet addresses and account passwords. Cryptocurrency platforms are attractive phishing targets because transactions are typically irreversible once completed. The relative novelty of crypto regulation makes users more likely to accept unusual verification requests as plausible.
Phishing scams grow more convincing every year, so share the types that have caught you off guard or that you think deserve more awareness in the comments.





