Most people assume that credit card fraud only happens to those who are careless or uninformed, but the reality is far more unsettling. Everyday habits that feel completely harmless can quietly hand over sensitive financial information to sophisticated scammers operating through digital networks, physical surveillance, and social engineering tactics. Understanding where these vulnerabilities hide is the first step toward protecting what matters most.
Public Wi-Fi Shopping

Connecting to an unsecured public network at a coffee shop or airport and then browsing retail sites or entering payment details is one of the most common ways card data gets intercepted. Cybercriminals use a technique known as a man-in-the-middle attack to position themselves between the user and the network, capturing everything transmitted in real time. Many shoppers assume that a password-protected café network is inherently safe, but that protection only prevents unauthorized connections and does nothing to shield data from others already on the same network. Any site without HTTPS encryption makes the situation significantly worse, as card numbers travel in plain, readable text.
Reusing Passwords
Using the same password across multiple accounts means that when one platform suffers a data breach, every other account sharing that credential becomes immediately vulnerable. Scammers purchase leaked login databases on dark web marketplaces and run automated tools that test those credentials across banking and retail sites within minutes. A shopping account and a banking app sharing the same password essentially creates a single point of failure for an entire financial life. Security researchers consistently find that credential stuffing attacks are responsible for a staggering volume of unauthorized credit card charges each year.
Clicking Email Links

Phishing emails have grown increasingly sophisticated, with many now perfectly mimicking the branding, tone, and formatting of major banks and retailers. Clicking a link inside one of these emails and entering payment information on the resulting page sends that data directly to a criminal rather than the intended company. Many of these fake sites use SSL certificates, meaning the browser displays a padlock icon that creates a false sense of security. The safest habit is to navigate directly to any financial or retail site by typing the address manually rather than following any link received by email.
Paying at Skimmed Terminals

Card skimming devices are installed directly onto ATMs, gas pump terminals, and retail card readers by criminals who return later to collect the stored data. These overlays are often designed so precisely that they are virtually indistinguishable from the legitimate hardware beneath them. A small pinhole camera installed nearby captures the PIN entry, giving fraudsters everything needed to replicate the card entirely. Contactless payment methods bypass the physical card reader altogether and offer a meaningful layer of protection against this type of attack.
Oversharing on Social Media

Posting photos of a new credit card to show off rewards tier status or a sleek card design exposes the card number, name, and expiration date to anyone who views the image. Even partially visible card details can be combined with other publicly available information to piece together enough data for unauthorized transactions. Scammers also mine social media profiles for answers to common security questions such as a mother’s maiden name, a first pet, or a hometown. Each piece of personal information shared publicly reduces the effort required to bypass account verification processes.
Ignoring Bank Statements
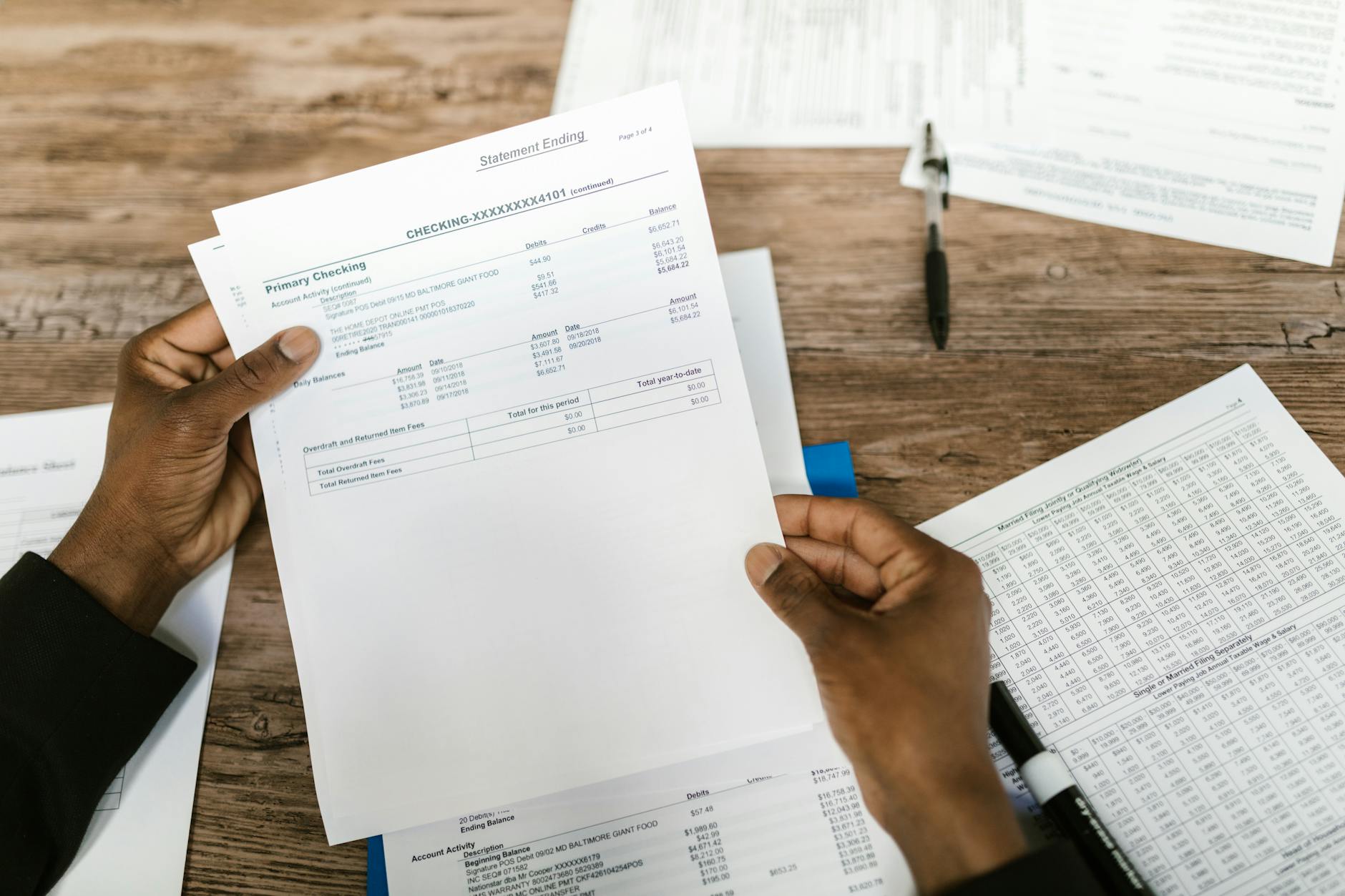
Failing to review monthly statements regularly allows small unauthorized charges to go unnoticed, which is precisely the strategy many fraudsters rely on. Scammers frequently test stolen card details with minor purchases of a few dollars to confirm the card is active before making larger withdrawals. Most card issuers have fraud reporting windows, and missing those deadlines can complicate the process of recovering lost funds. Setting up real-time transaction notifications through a banking app is one of the most effective ways to catch suspicious activity the moment it occurs.
Auto-Saving Card Details

Storing credit card information in browsers, retail accounts, and apps significantly expands the number of places where that data can be compromised. When any one of those platforms experiences a breach, saved payment details become part of the exposed dataset alongside email addresses and shipping information. Malware designed to extract stored browser credentials is widely distributed through infected downloads and compromised websites. Manually entering payment details for each transaction is more cumbersome but substantially reduces the attack surface available to cybercriminals.
Using Debit for Online Purchases

Debit cards draw funds directly from a checking account, meaning fraudulent charges cause an immediate and tangible loss of available cash. Credit cards, by contrast, are governed by stronger consumer protection laws that make it easier to dispute unauthorized charges without losing access to real funds during the investigation. The liability window for reporting unauthorized debit card transactions is also considerably shorter, placing more pressure on the cardholder to act quickly. Many financial experts recommend reserving debit cards exclusively for ATM withdrawals and using credit cards for all online spending.
Answering Verification Calls

Vishing scams involve criminals calling victims while impersonating bank fraud departments, creating urgency around a supposed suspicious transaction. The caller already possesses partial card information obtained from a previous data breach, which lends the interaction an air of legitimacy. During the call, the victim is typically asked to confirm the full card number, expiration date, or the three-digit security code on the back. Legitimate bank representatives never need a customer to read back their full card details because that information is already on file.
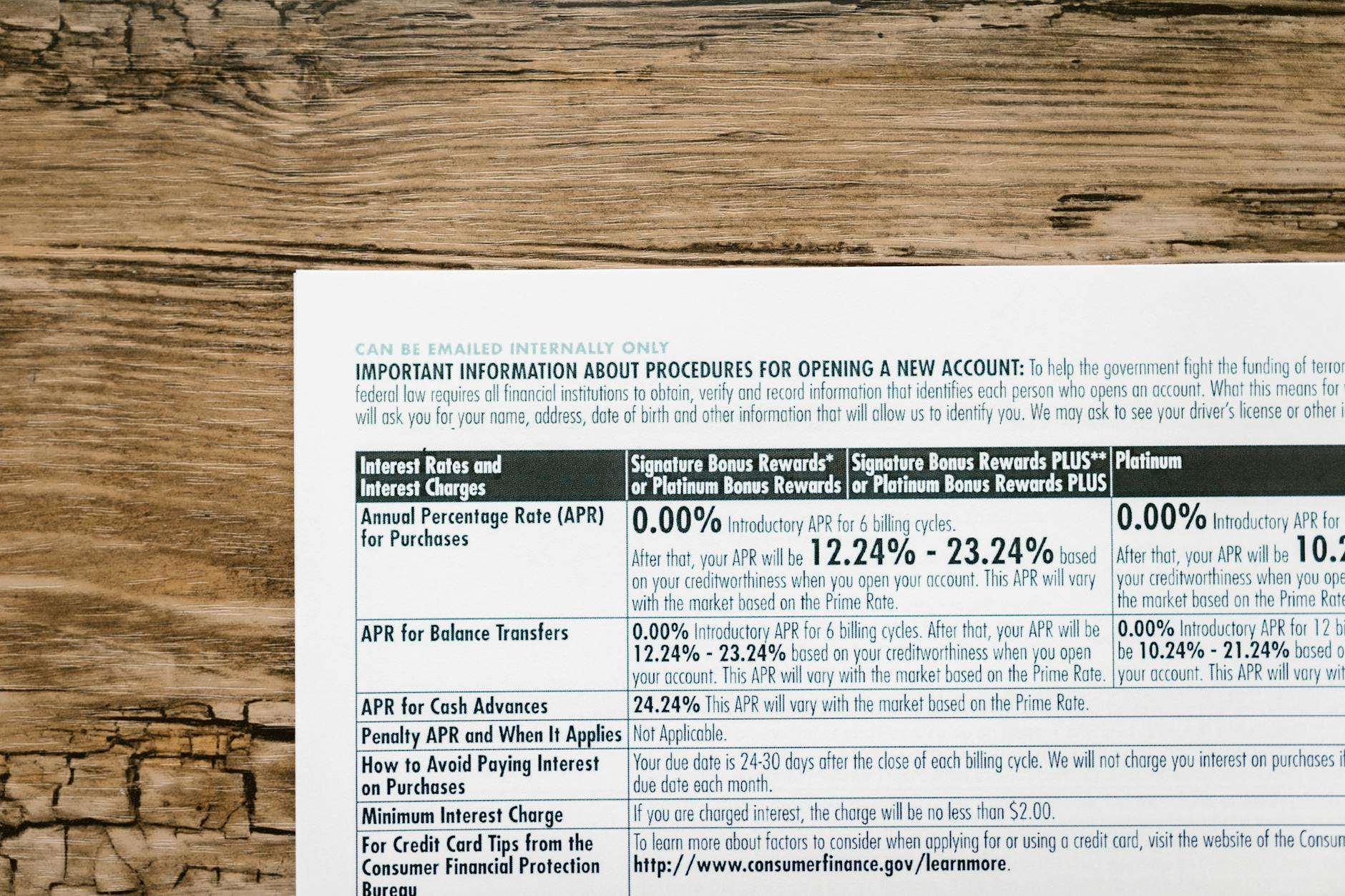
Using Unsecured Websites
Shopping on websites that lack proper HTTPS encryption transmits payment data across the internet without any protective layer, making interception relatively straightforward. The padlock symbol in the browser address bar indicates an encrypted connection and should be the minimum standard before entering any financial information. Beyond encryption, some sites are built specifically to collect payment details with no intention of fulfilling an order. Checking for verified trust seals, reading reviews on independent platforms, and confirming contact information are all steps worth taking before purchasing from an unfamiliar retailer.
Tossing Card Receipts

Physical receipts discarded in public trash cans or even left on restaurant tables can contain enough partial card information to assist a scammer who has obtained additional details elsewhere. Some older or poorly configured point-of-sale systems still print full card numbers or expiration dates on customer copies in violation of data standards. Dumpster diving remains an active and surprisingly effective tactic used by low-tech fraudsters operating in busy commercial areas. Shredding any document that contains card details, account numbers, or personal identifiers before disposal eliminates this vulnerability entirely.
Connecting to Fake Hotspots

Criminals set up rogue Wi-Fi hotspots in busy public spaces using common names like “Airport Free Wi-Fi” or “Hotel Guest Network” to lure unsuspecting users into connecting. Once connected, all traffic passing through that network is fully visible to whoever controls the hotspot, including any payment pages visited during that session. Devices that are set to automatically join open networks are particularly at risk because the connection can happen without any deliberate action from the user. A virtual private network encrypts outgoing traffic and provides a reliable layer of protection even when connecting through an unknown or untrusted hotspot.
Sharing Card Photos for Refunds
Some fraudulent customer service schemes ask buyers to photograph both sides of their card as part of a supposed verification or refund process. No legitimate retailer, payment processor, or financial institution requires a photograph of a physical card to process a return or confirm identity. The image captures all the information needed to make online purchases, and once sent through a messaging app or email, that data is difficult to contain or delete permanently. Any request to send a card photo through any channel should be treated as an immediate red flag and reported to the card issuer.
Share your thoughts on these everyday vulnerabilities in the comments.





