Most people think of identity theft as a digital crime carried out by faceless hackers working through computer screens, but a significant proportion of identity fraud begins at the kerb outside a family home. Criminals known as dumpster divers systematically go through residential and commercial rubbish looking for fragments of personal information that can be assembled into a complete identity profile. The terrifying reality is that the average household discards dozens of useful documents and objects every single week without giving their contents a second thought. Understanding exactly what thieves are looking for is the first and most powerful step toward protecting everything you have built.
Bank Statements
Printed bank statements contain an extraordinary concentration of personal financial data including account numbers, sort codes, transaction histories, and the full legal name and address of the account holder. A single statement handed to a skilled fraudster provides enough raw material to attempt account takeover, apply for credit in the account holder’s name, or craft highly convincing phishing communications. Many people accumulate months of statements before throwing them out in a single batch which only increases the value of what ends up in the bin. Shredding every statement into cross-cut fragments before disposal is the minimum acceptable standard for protecting this category of document.
Utility Bills
Gas, electricity, water, and broadband bills carry a person’s full name, home address, account reference number, and often direct debit banking details in a single printed document. Utility bills are among the most commonly accepted proof of address documents used by financial institutions, government agencies, and rental companies making them extraordinarily useful to identity thieves. A fraudster in possession of a recent utility bill can use it to open new accounts, redirect mail, or pass identity verification checks at a range of service providers. Even bills that appear to contain nothing sensitive beyond a name and address should be shredded before they reach the general waste stream.
Prescription Labels

Pharmacy prescription labels attached to medicine bottles and packaging contain the patient’s full name, home address, date of birth, prescribing doctor’s name, medication name, dosage, and pharmacy details all in one place. This combination of medical and personal data is valuable both for identity fraud and for more targeted crimes including burglary, since knowing someone takes certain medications can reveal information about their age, health vulnerabilities, and daily routine. Prescription information can also be used to fraudulently obtain medications or to manipulate insurance records. Every prescription label should be removed and shredded or rendered illegible before the packaging is placed in recycling or general waste.
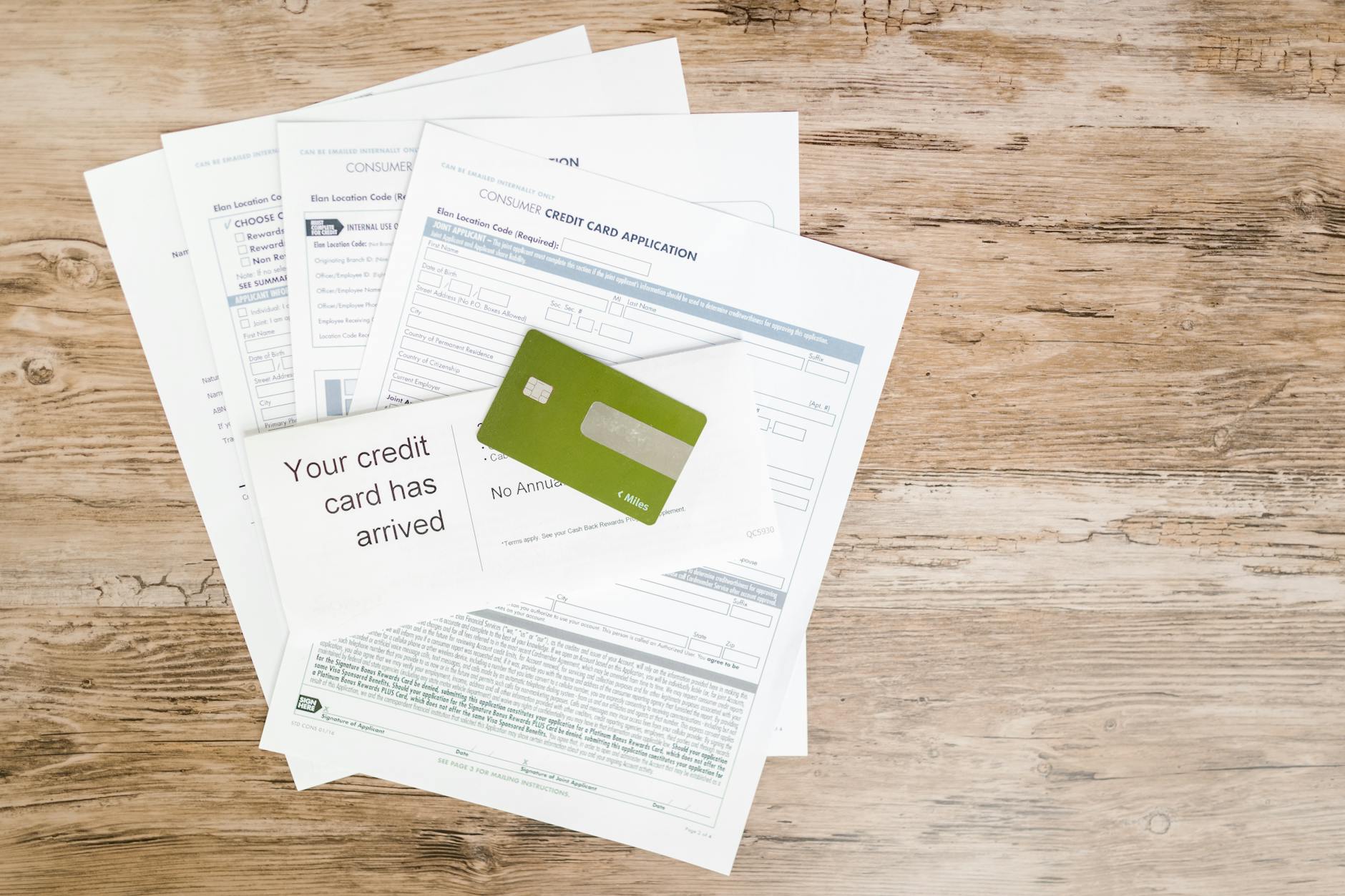
Credit Card Offers

Pre-approved credit card offers and loan invitations sent through the post contain enough personal and financial data for a thief to complete an application in the recipient’s name with minimal additional effort. These mailers frequently include a pre-filled application form, the recipient’s name, address, and in some cases a reference number linked to their credit profile. A criminal who intercepts one of these offers from the rubbish can apply for the card, redirect it to a different address, and begin spending before the legitimate account holder has any awareness that new credit has been opened in their name. Every pre-approved credit offer should be shredded in its entirety including the reply envelope.
Old Passports

An expired passport remains one of the most powerful identity documents in existence even after it has passed its validity date because it contains a confirmed photograph, full legal name, date of birth, place of birth, nationality, and a unique document number. Criminals use expired passports to build synthetic identities by combining the genuine biographical information with fabricated or stolen supporting documents. In some fraud schemes the photograph is replaced while the biographical data page is used as a foundation for a counterfeit document. Expired passports should be stored securely or destroyed through a specialist document destruction service rather than placed in household rubbish.
Payslips

A payslip contains an employee’s full name, home address, national insurance or tax identification number, employer’s name and address, salary details, bank account information, and tax code all in a single document. This combination of employment, financial, and government identification data gives a fraudster almost everything they need to impersonate someone for employment-related fraud, benefit claims, or financial account applications. Employers are legally required to provide payslips but employees are under no obligation to retain physical copies once they have been reviewed and reconciled. Every payslip regardless of how old it is should be cross-cut shredded before disposal rather than placed whole into any waste stream.
Junk Mail

Generic addressed junk mail including catalogues, promotional letters, and subscription offers may appear to contain nothing sensitive but still carries a person’s confirmed name and address in a deliverable format. A collection of junk mail items allows a thief to establish that a particular person lives at a particular address which is useful for mail redirection fraud, targeted phishing, and social engineering attacks. High volumes of addressed promotional mail also signal to criminals that an address is occupied by someone who shops, borrows, or holds accounts with multiple organisations. Any addressed mail regardless of its apparent commercial irrelevance should be shredded before disposal to prevent address confirmation falling into the wrong hands.
Old Driving Licences

An expired or superseded driving licence contains a photograph, full legal name, date of birth, home address, licence number, and vehicle entitlement categories that remain personally identifying long after the document has been replaced. Driving licence numbers in many countries follow a predictable format derived from the holder’s name and date of birth meaning that even a damaged or partial licence can yield a reconstructable identifier. Fraudsters use driving licences as the photographic proof of identity component in multi-document identity fraud schemes. Physical driving licences should be destroyed using a cross-cut shredder or returned to the issuing authority rather than placed in household waste.
Loyalty Card Receipts
Supermarket and retail loyalty card receipts often print the partial card number, the cardholder’s first name, accumulated points balance, and purchasing history on a document that most people discard immediately at the checkout or bin when emptying pockets. While a single loyalty receipt contains limited standalone value the data it carries can be used to facilitate account takeover of the associated loyalty programme which in turn may be linked to a payment card or personal email address. High-value loyalty accounts containing travel points, cashback balances, or gift card credits are increasingly targeted by fraudsters who regard them as a form of transferable currency. Loyalty receipts should be treated with the same discretion as payment card receipts and disposed of securely.
Insurance Documents

Home, car, health, and life insurance documents contain a person’s full name, address, date of birth, policy numbers, coverage details, vehicle registration numbers, and in some cases national identification numbers all within a single package. Insurance policy information can be used to file fraudulent claims, cancel existing policies to create financial disruption, or provide supporting documentation in a broader identity fraud scheme. Vehicle insurance documents in particular contain registration details that criminals can use in combination with other information to commit motoring fraud. All insurance correspondence including renewal notices, policy schedules, and cancellation letters should be shredded before disposal regardless of how old the policy is.
Boarding Passes

A paper boarding pass or printed booking confirmation contains the passenger’s full name, frequent flyer number, booking reference code, departure and arrival airports, seat number, and travel date in printed form. The booking reference code printed on a boarding pass can be entered directly into airline websites to access the full itinerary, personal contact details, and passport information stored against the booking. Criminals who obtain a boarding pass from rubbish can use the reference code to access travel records, accumulate frequent flyer miles fraudulently, or gather personal data for use in targeted fraud. Boarding passes should be shredded after the journey rather than left in seat pockets, hotel bins, or airport waste bins.
Tax Returns

Paper tax returns and supporting documents contain a person’s national tax identification number, full name, address, employment details, income figures, bank account information, and employer identifiers making them among the most comprehensively damaging documents that can end up in the wrong hands. Tax identity fraud in which a criminal files a return in someone else’s name to claim a fraudulent refund is one of the fastest growing forms of identity crime in multiple countries. Even partial or draft tax documents contain enough sensitive data to cause significant harm if intercepted. Tax documents should be retained for the legally required period in secure storage and then destroyed using a cross-cut shredder or a certified document destruction service.
Medicine Packaging

Empty boxes, blister packs, and outer cartons from prescription and over-the-counter medications are routinely thrown into household recycling without their labels being removed. Beyond the prescription label issue the packaging itself can reveal detailed information about a person’s health conditions, treatment history, and medical provider relationships that can be exploited in insurance fraud and medical identity theft. Medical identity theft in which a criminal uses another person’s identity to obtain healthcare, medications, or insurance benefits is a growing category of fraud with serious consequences for the victim’s medical records and financial standing. All medicine packaging should have identifying labels removed and destroyed before the packaging is placed in any waste or recycling stream.
Old Cheques
Cancelled, voided, and unused cheques from closed accounts remain dangerous documents even when the account they were drawn on no longer exists. A cheque carries the account holder’s full name, home address, bank name, sort code, and account number in a format specifically designed to facilitate financial transactions. Criminals with access to this information can create counterfeit cheques, attempt electronic transfers, or use the banking details as part of a broader account takeover scheme. Old cheque books from closed accounts should be destroyed completely using a cross-cut shredder rather than placed whole into recycling or general waste.
Gym Membership Forms

Paper gym membership applications and renewal forms contain a member’s full name, home address, date of birth, emergency contact details, health information, and direct debit banking data in a single document. Fitness centres frequently discard outdated membership forms in general commercial waste without applying any document security protocols making them accessible to anyone willing to search through business bins. The combination of personal, health, and banking information on a single form makes this document category more valuable to fraudsters than most members would ever anticipate. If a gym or fitness provider asks you to complete a paper form request confirmation that the document will be stored securely and destroyed appropriately when no longer needed.
Children’s School Documents

Reports, permission slips, enrolment forms, and school correspondence contain a child’s full name, home address, date of birth, and parent or guardian details which together form the foundation of a child identity that can be fraudulently exploited for years. Child identity theft is particularly insidious because it often goes undetected until the victim attempts to open their first bank account or apply for credit as a young adult and discovers an existing fraudulent history. Children have clean credit profiles with no existing accounts making them attractive targets for long-term identity fraud schemes. All school documentation containing personal details should be treated with the same seriousness as adult financial documents and shredded before disposal.
Old Mobile Phones
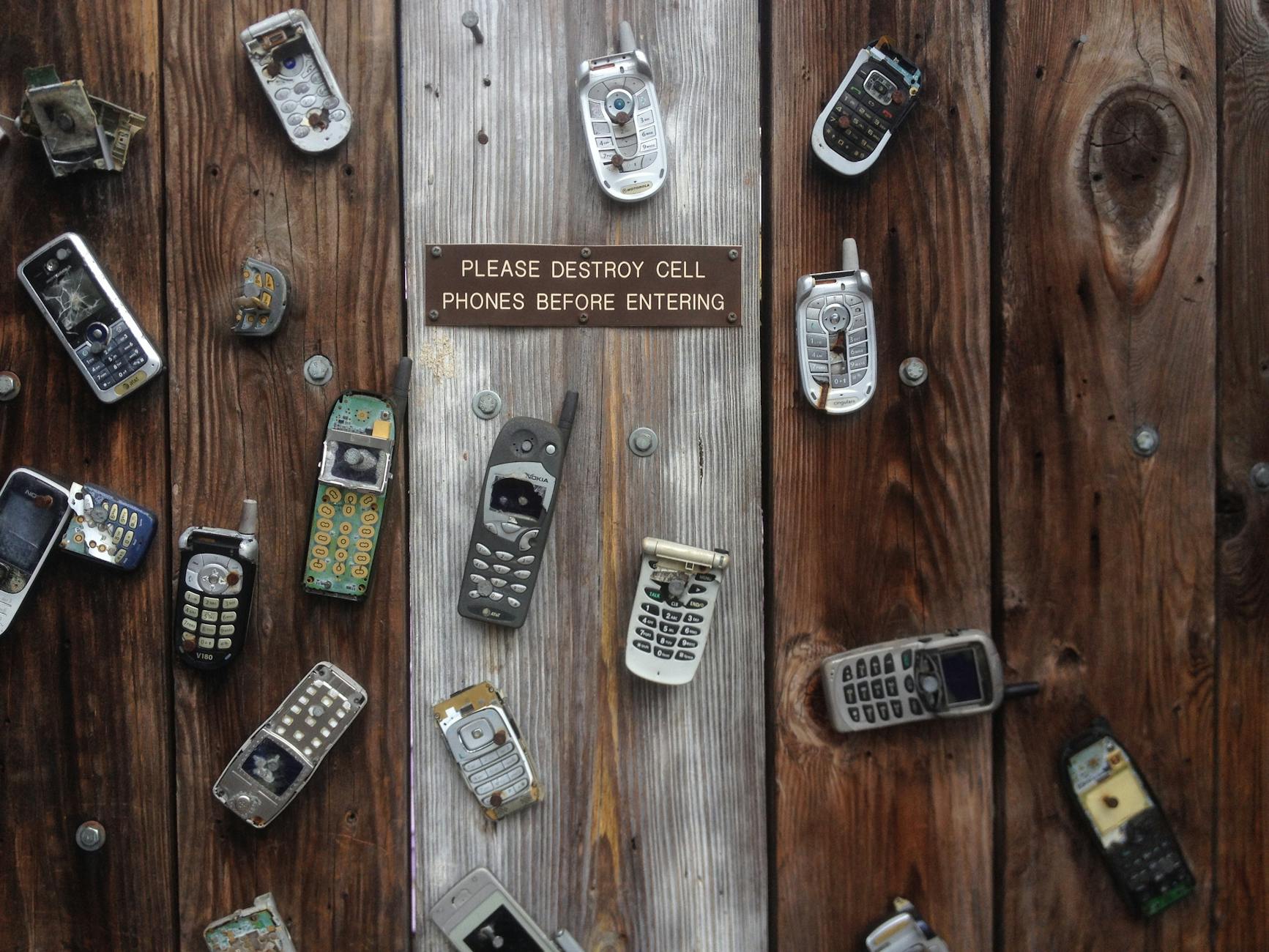
A discarded mobile phone without a full factory reset retains contacts, messages, emails, photographs, saved passwords, banking app data, and browsing history that collectively represent one of the most comprehensive personal data profiles imaginable. Even phones with cracked screens, depleted batteries, or apparent hardware failures can have their storage accessed by criminals using relatively inexpensive recovery tools. SIM cards removed from old phones and placed in the bin separately retain call logs, text messages, and contact lists in recoverable form. Every mobile phone should receive a certified factory reset before disposal and SIM cards should be physically cut or destroyed rather than discarded intact.
Mortgage Documents

Mortgage application forms, offer letters, and annual statements contain a borrower’s full name, address, date of birth, national identification number, income details, property valuation, loan amount, and lender account reference in a single document. Property fraud in which a criminal attempts to transfer ownership of a home or remortgage a property using stolen identity documents is among the most financially devastating forms of identity crime a person can experience. Even older mortgage documents from properties that have since been sold retain personal data that remains useful to identity fraudsters. All mortgage paperwork should be retained in secure storage for a minimum period after a property transaction and then destroyed through a certified shredding service.
Delivery Packaging

Parcels and packages from online retailers carry the recipient’s full name, home address, and sometimes their telephone number on adhesive labels that remain legible long after the contents have been removed. A collection of delivery labels found in a recycling bin confirms that a specific named individual lives at a specific address and may reveal their purchasing habits, subscriptions, and lifestyle patterns through the branding of the sender. Some delivery labels also include partial order reference numbers that can be used to access account details through retailer customer service channels. All delivery labels should be removed from packaging and shredded or rendered illegible before the cardboard is placed in recycling.
Old Diaries and Planners
Paper diaries, personal planners, and address books contain handwritten records of appointments, contacts, passwords, account numbers, personal reflections, and relationship details that provide a deeply intimate map of a person’s life. A discarded diary gives a fraudster not only data points but a contextual understanding of a person’s habits, relationships, and routines that can be used to craft highly convincing impersonation attempts. Address books in particular contain contact networks that can be exploited to make fraudulent approaches to a victim’s family, friends, or colleagues on their behalf. Old diaries and planners should be shredded page by page rather than placed whole in a bin where their handwritten contents remain fully readable.
Reward Programme Statements

Printed statements from air miles programmes, hotel loyalty schemes, cashback cards, and retail reward accounts show accumulated balances, transaction histories, membership numbers, and the personal details registered to the account. High-value reward balances represent real transferable financial worth and criminals who obtain the membership number and personal details from a discarded statement can attempt account takeover to drain accumulated points or miles. Some reward programme statements also include partial payment card details linked to the account. These documents should be treated with the same level of security as bank statements and destroyed completely before disposal.
Old Spectacles Prescriptions

An optical prescription contains the patient’s full name, home address, date of birth, and detailed vision measurements that can be used alongside other documents in medical identity theft schemes. Eye care prescriptions are also useful to fraudsters building a synthetic identity because they represent an officially issued medical document that can support false claims about a person’s identity, age, or address. Some optical prescriptions are issued on headed paper carrying the practice’s registration details which adds an element of official legitimacy to the document. Optical prescriptions that are no longer current should be shredded before disposal rather than placed into recycling along with other paper waste.
Pension Statements

Annual pension statements and retirement account letters contain a person’s full name, home address, national insurance or tax identification number, pension scheme reference, employer details, and projected retirement income figures. Pension fraud in which criminals use stolen identity information to redirect retirement savings or make fraudulent claims against pension funds has increased significantly in recent years. The long time horizon of pension savings means that fraudulent activity can go undetected for extended periods before it comes to the attention of either the scheme or the victim. All pension correspondence should be stored securely in a locked location and destroyed using a cross-cut shredder when it is no longer needed for reference purposes.
Store Card Statements

Retail store card statements carry account numbers, credit limits, payment history, and personal details in a format that many people consider less sensitive than a bank statement but which contains equally exploitable financial data. Store card accounts are frequently used as entry points into broader credit fraud because their verification requirements are sometimes less stringent than those applied by high street banks. A fraudster who obtains a store card statement can attempt to change the address on the account, request a credit limit increase, or use the account details as supporting documentation in a wider identity fraud application. Store card statements should be shredded with the same diligence applied to primary bank account correspondence.
Old CV or Resume Copies
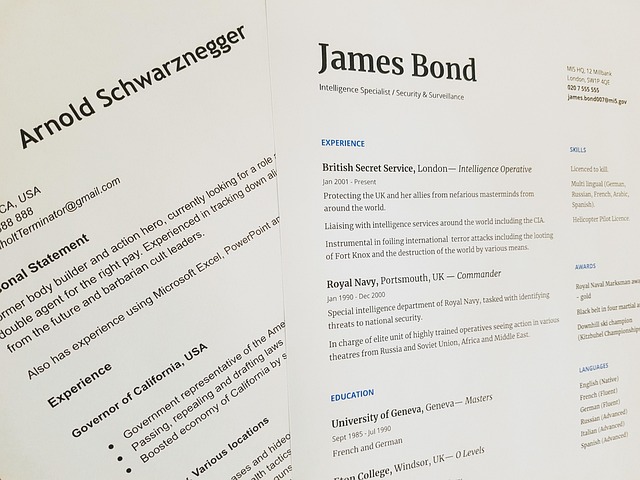
A printed curriculum vitae contains a person’s full name, home address, personal email address, telephone number, date of birth, employment history, educational qualifications, professional references, and sometimes a personal photograph all assembled in a single comprehensive document. Criminals who obtain a CV from discarded workplace or home waste gain an extraordinarily detailed personal profile that requires minimal supplementation to support a full identity fraud attempt. CV data is also valuable for crafting targeted spear phishing attacks using the professional context and relationship details the document contains. Any printed copy of a CV or resume that is no longer needed should be cross-cut shredded regardless of how old it is or how many roles have changed since it was printed.
Medical Test Results

Printed results from blood tests, scans, screenings, and other diagnostic procedures carry a patient’s name, date of birth, address, patient identification number, GP or specialist details, and sensitive health data that can be used in medical identity fraud. Medical identity theft allows criminals to obtain prescriptions, claim health insurance benefits, or access healthcare services using another person’s verified patient identity. Victims of medical identity theft frequently discover the crime only when their own medical records have been contaminated with incorrect information relating to the fraudster’s treatments. All medical correspondence including test results, referral letters, and appointment confirmations should be shredded before disposal to prevent this particularly harmful category of fraud.
Voter Registration Cards
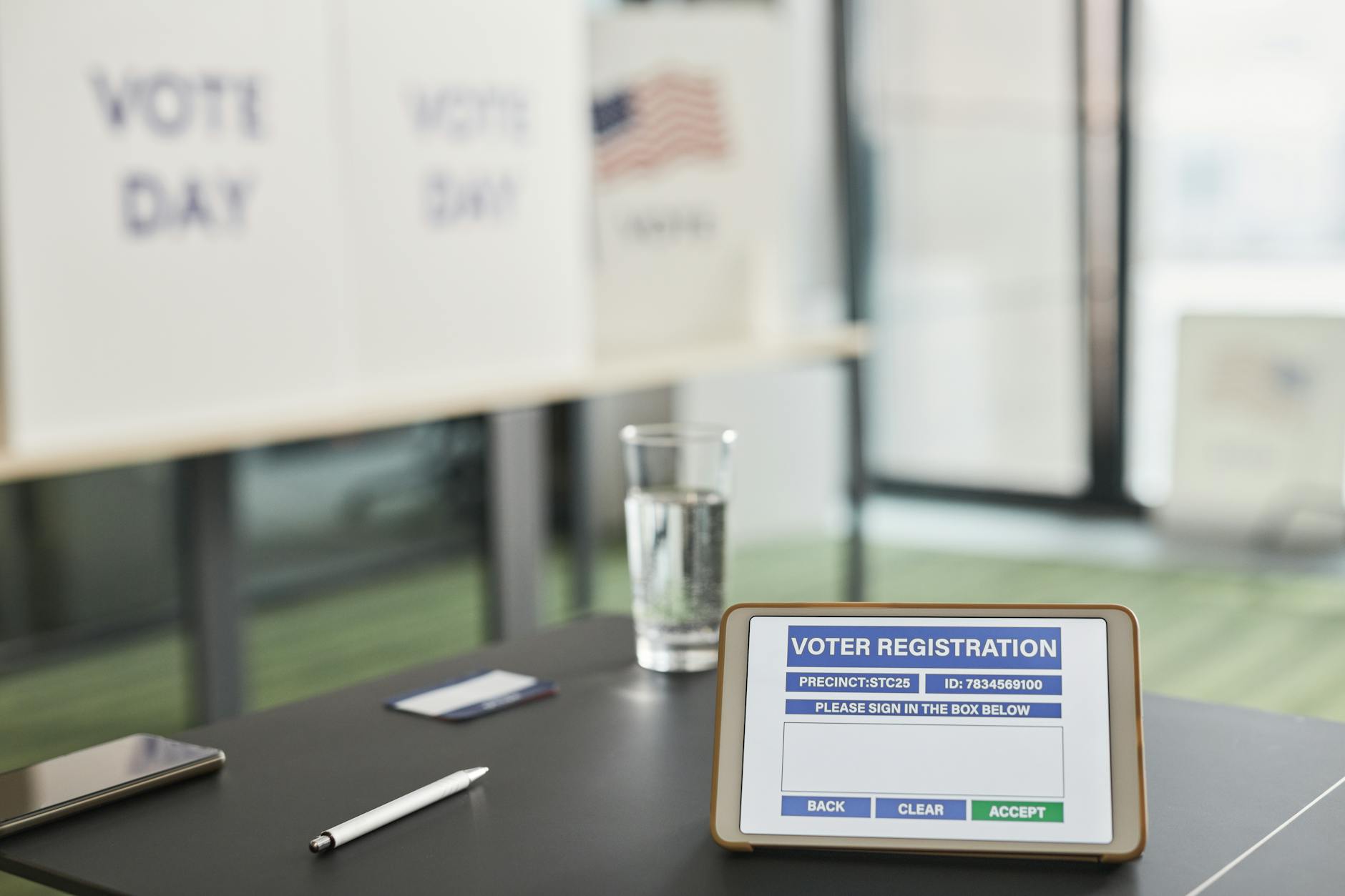
Voter registration documents confirm a person’s full legal name, home address, and registered constituency or district in an officially issued format that carries significant credibility as proof of identity. This document is accepted as address verification by a range of financial and government service providers making it useful to fraudsters assembling a supporting identity document portfolio. Voter registration data combined with other discarded documents can enable a criminal to pass multi-point identity checks at banks, lenders, and government agencies. Voter registration documents that have been superseded by an updated version should be shredded before disposal rather than placed in recycling with general paper waste.
Solicitor and Legal Letters

Correspondence from solicitors, notaries, and legal professionals contains case reference numbers, property details, financial settlement figures, estate information, and deeply personal legal circumstances that represent a goldmine of exploitable data for sophisticated fraudsters. Legal letters involving property transactions, wills, divorce proceedings, or business agreements contain particularly sensitive financial and personal information that can support property fraud, inheritance fraud, and targeted financial crime. The professional letterhead and formal language of legal correspondence also lends credibility to documents used in impersonation schemes. All legal correspondence should be retained in a secure location while it remains relevant and destroyed through a certified document shredding service when it is no longer required.
Handwritten Notes
Scraps of paper carrying handwritten account numbers, passwords, PIN codes, security question answers, and website login details are discarded into household bins with alarming regularity by people who write down sensitive information as a memory aid. A single note bearing a PIN alongside the name of a bank or a password next to a website address provides immediate and direct access to the associated account without requiring any further fraud infrastructure. Many people also write telephone numbers alongside the names of banks, doctors, or employers which helps a criminal map the victim’s account and service relationships. Any handwritten note containing numerical codes, passwords, or account references should be shredded or physically destroyed rather than crumpled and placed in a bin where the writing remains legible.
Mortgage Valuation Reports

Property valuation reports commissioned during a mortgage application contain the full address and description of a property, its estimated market value, structural details, and the applicant’s personal and financial information in a single professionally produced document. This combination of property and personal data is particularly valuable to criminals engaged in title fraud which involves fraudulently transferring the ownership of a property or using the property as security for loans taken out without the owner’s knowledge. Valuation reports are often produced as multiple copies and supplementary pages that are easy to lose track of and discard casually at the end of a property transaction. Every copy of a property valuation report should be stored securely and destroyed through a certified service when the property transaction is complete and the retention period has passed.
Old SIM Cards

A SIM card removed from a replaced mobile phone and placed in a drawer or a bin retains a registered telephone number, call logs, text message history, and contact information that can be extracted using widely available card reading equipment. In many countries a SIM card is registered to a specific individual’s identity meaning that a recovered SIM can be used to facilitate SIM swap fraud in which criminals redirect a victim’s phone number to a device they control. Phone number access is increasingly used as a two-factor authentication method by banks and email providers making a recovered SIM card a potential key to a wide range of secured accounts. Old SIM cards should be physically cut into multiple pieces before disposal to ensure that the chip cannot be read or reused by anyone who recovers them from household waste.
If any of these items are currently making it into your bin intact or you have taken steps to protect yourself that others might benefit from knowing, share your experience in the comments.





