Online scammers have grown increasingly sophisticated in their methods and their tactics can be difficult to spot at first glance. Recognising the early warning signs before any damage is done is one of the most valuable digital skills a person can have today. The following list covers thirty subtle indicators that someone may be attempting to manipulate or defraud you online. Staying informed about these patterns is the first step toward protecting your personal and financial security in an always-connected world.
Urgency Language

Messages that push you to act immediately are a classic manipulation technique used by fraudsters across every platform. The pressure to respond within hours or risk losing something creates panic that overrides rational thinking. Legitimate organisations rarely demand instant decisions on financial or personal matters. This artificial time pressure is designed to prevent you from pausing to verify the situation independently.
Unusual Sender Address

An email or message may appear to come from a trusted brand but the actual sending address often reveals subtle inconsistencies. Scammers frequently use domains that closely mimic real company addresses with a single letter changed or an extra word added. Hovering over or tapping the sender field usually exposes the true origin of the communication. Trusted institutions maintain consistent and verifiable contact addresses that match their official websites.
Vague Greetings

Personalised communication is standard practice for any legitimate business that holds your account information. Generic openers such as “Dear Customer” or “Hello User” suggest the message was sent in bulk without any real knowledge of who you are. Real banks and service providers address you by your registered name in direct correspondence. This impersonal approach is a reliable early indicator that something is not right.
Prize Notifications

Being told you have won a competition you never entered is one of the most enduring scam formats in digital communication. These messages typically request personal details or a small fee before the supposed prize can be released. No legitimate lottery or giveaway requires upfront payment from a winner. The appeal of unexpected financial gain is precisely what makes this tactic persistently effective.
Requests for Passwords
No genuine organisation ever asks for your password through email text message or chat. This request alone is a definitive red flag regardless of how official the accompanying message appears. Companies with secure systems have no operational need to obtain your login credentials directly from you. Sharing a password in response to any unsolicited contact can result in immediate account compromise.
Mismatched Links

A hyperlink may display one web address while actually directing you to a completely different destination. Scammers craft these deceptive links to mimic the appearance of real websites while capturing any information you enter. Checking the actual URL before clicking by hovering over the link is a simple and effective protective habit. Secure official websites consistently use verified domains that align with their brand name.
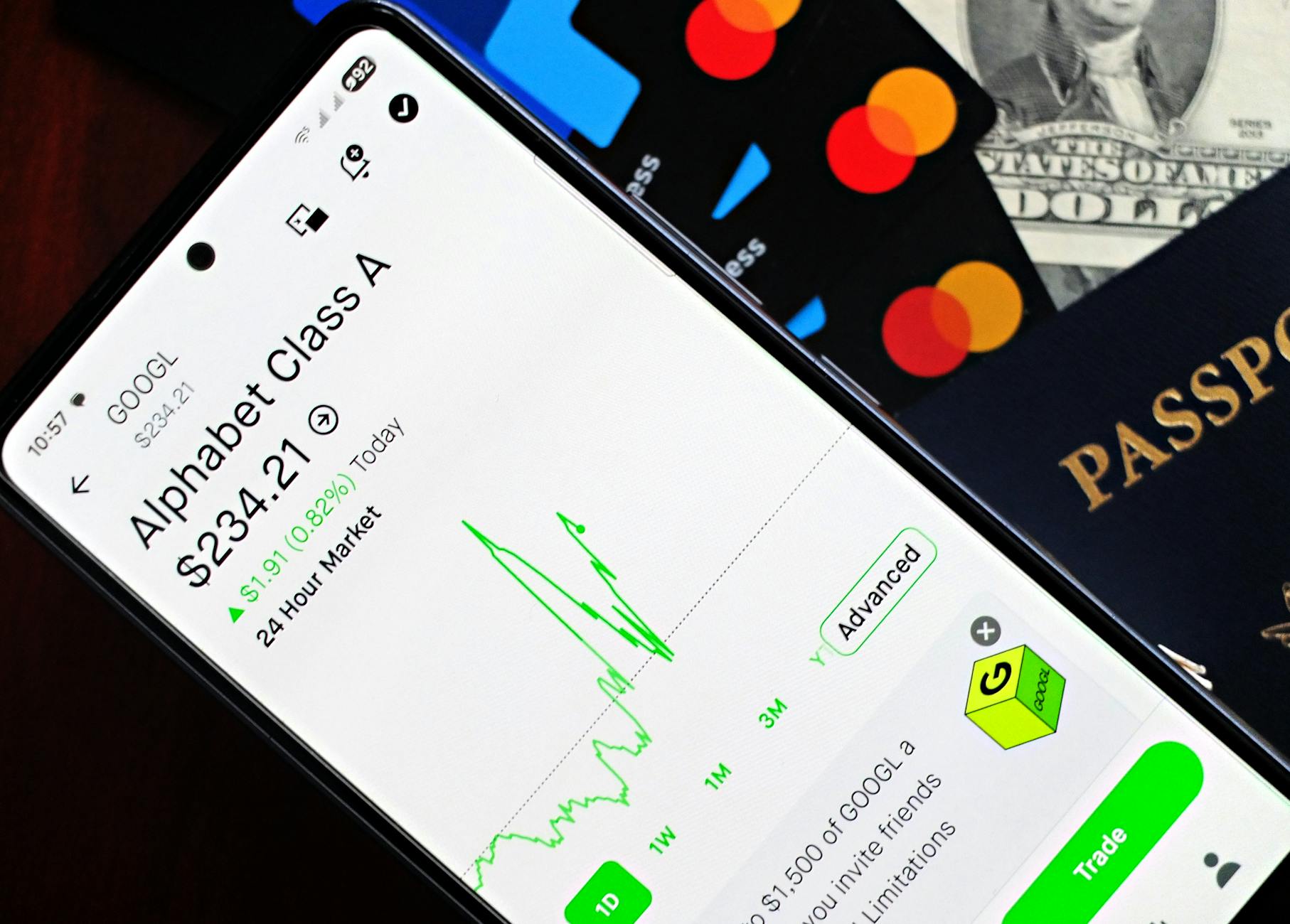
Too Good Offers

Investment opportunities or product deals that promise extraordinary returns with minimal risk are almost always fraudulent. The contrast between the promised reward and the apparent low effort required should trigger immediate scepticism. Professional financial advisors and legitimate retailers operate within realistic and regulated boundaries. Offers that seem implausibly generous are typically designed to cloud judgement through excitement.
Poor Grammar

Professionally written communications from established companies go through editorial review before reaching customers. Messages riddled with spelling mistakes awkward phrasing or grammatical inconsistencies suggest a lack of legitimate infrastructure. While minor errors occur even in real correspondence a pattern of poor language quality is a meaningful warning sign. Many scam operations are run from regions where the target language is not the primary one spoken.
Unverified Profiles

Social media accounts with very few posts a recently created date or unusually low follower counts should be approached carefully. Fraudsters create fake profiles to build trust before initiating requests for money personal data or sensitive information. Authentic individuals and businesses develop their online presence over time with consistent and verifiable activity. Scrutinising a profile before engaging with requests from it is a reasonable precaution.
Unexpected Invoices

Receiving a bill or payment confirmation for a transaction you never made is a tactic used to prompt confused responses. Scammers rely on the recipient contacting them to dispute the charge and in doing so handing over personal details. A genuine billing error from a real company can be verified independently through official contact channels. Never use the phone number or link provided within a suspicious invoice to query it.
Sob Stories

Elaborate personal narratives involving sudden illness stranded travel or unexpected tragedy are common emotional manipulation tools. These stories are crafted specifically to activate empathy and reduce the critical thinking that would otherwise detect the fraud. Genuine requests for help from known contacts can always be verified through a direct phone call or video chat. The more emotionally compelling an unsolicited story is the more carefully it deserves to be examined.
Government Impersonation
Messages claiming to be from tax authorities immigration departments or law enforcement are designed to trigger fear and compliance. Real government bodies communicate through official postal channels or verified digital portals rather than unsolicited emails or texts. Threats of immediate legal action or financial penalties are particularly common in this category of scam. Independently contacting the relevant government body through official numbers is the appropriate response to any such message.
Unusual Payment Methods

Any request for payment through gift cards wire transfers cryptocurrency or peer-to-peer apps should raise immediate concern. These payment types are favoured by scammers because they are difficult or impossible to reverse once completed. Regulated businesses and government entities do not request payment through unconventional or untraceable methods. The insistence on a specific payment type outside of standard channels is a strong indicator of fraudulent intent.
Cloned Websites

Fraudulent websites are often built to look almost identical to legitimate ones including logos colour schemes and navigation structures. Small differences in the URL such as an additional hyphen or a different domain extension are the most common giveaways. Bookmarking official websites and accessing them directly rather than through links reduces exposure to this technique. Security indicators such as valid HTTPS certificates provide some assurance but are not sufficient verification on their own.
Account Verification Requests

Unsolicited messages asking you to confirm your identity or verify your account details are frequently part of phishing operations. These requests often mimic the design of communications from well-known platforms to appear credible. Logging into your account directly through the official app or website is always the correct way to address any genuine account issue. Responding to these messages by clicking embedded links risks exposing login credentials to third parties.
Romantic Advances

Online romantic interest from someone who escalates a relationship quickly and then requests money is a well-documented fraud pattern. These connections are often cultivated over weeks or months to build a sense of genuine emotional attachment. The eventual financial request is typically framed within a crisis narrative that plays on the established bond. This form of fraud causes both financial and significant emotional harm to its targets.
Unusual App Permissions
Applications that request access to contacts location cameras or microphones beyond what their function requires present a privacy risk. Malicious apps are sometimes designed to harvest data under the guise of offering a useful or entertaining service. Reviewing the permissions requested during installation is an important step before accepting any app onto a device. Official app stores provide some level of vetting but do not catch every problematic application.
Forwarded Chain Messages

Messages urging you to share content with others to claim a reward or avoid a penalty are often used to spread misinformation or harvest contact data. The forwarding mechanism allows scammers to reach a wide audience through trusted personal networks. Legitimate promotions and warnings do not require viral distribution among your contacts to be valid. Pausing before forwarding any message to consider its origin and plausibility is a healthy digital habit.
Fake Job Offers

Unsolicited employment opportunities promising high pay for minimal qualifications or remote work with no interview process are frequently fraudulent. These offers often require the target to pay upfront for training equipment or background checks before work begins. Genuine employers conduct formal recruitment processes and do not request financial contributions from candidates. Verifying a company through independent research before engaging with any job offer is essential.
Tech Support Calls

Unsolicited calls or pop-up messages claiming your device has been compromised and offering immediate technical assistance are a widespread fraud method. The caller or message typically requests remote access to your computer to supposedly resolve the issue. Granting this access allows the scammer to install malicious software or access stored personal and financial information. Major technology companies do not proactively contact users in this manner about device security issues.
Overpayment Scams

In this scheme a buyer sends a payment that exceeds the agreed amount and then asks the seller to refund the difference. The original payment is subsequently reversed or revealed to be fraudulent leaving the seller without both the money and the goods. This tactic is common in peer-to-peer marketplaces and private sale platforms. Any overpayment situation regardless of the explanation offered warrants extreme caution before any funds are returned.
Sudden Inheritance

Notifications informing you of an unclaimed inheritance from a distant or unknown relative typically require personal details or fees to proceed. These messages are a variation of advance fee fraud and have been in circulation in various forms for decades. Legitimate inheritance processes are conducted through legal channels and do not begin with unsolicited digital messages. The combination of a large promised sum and a request for upfront costs is a defining characteristic of this fraud type.
QR Code Redirects

QR codes placed in public spaces or sent digitally can direct users to malicious websites designed to steal information or install harmful software. Unlike typed URLs these codes cannot be read by the human eye before scanning which makes them particularly effective as a deceptive tool. Some security-conscious mobile devices offer a preview of the destination URL before fully loading the page. Scanning codes only from sources you have independently verified reduces the risk of being redirected to a fraudulent destination.
Impersonated Friends

Receiving a message from a known contact asking for urgent financial help or unusual personal information can indicate their account has been compromised. Scammers access genuine accounts and use them to send targeted messages to the contact list benefiting from the existing level of trust. A quick direct call to the person through a known phone number is the fastest way to determine whether the request is legitimate. Unusual tone vocabulary or behaviour in written messages from a familiar contact should prompt verification before any response.
Subscription Traps
Free trials that require credit card details upfront and transition automatically into paid subscriptions are a common source of unexpected financial loss. The terms governing the automatic renewal are often buried in lengthy documents that most users do not read in full. Monitoring bank statements regularly helps identify these charges before they accumulate significantly. Legitimate subscription services make their billing terms prominent and provide straightforward cancellation processes.
Duplicate Charity Appeals

Fraudulent charity campaigns frequently emerge in the aftermath of natural disasters humanitarian crises or viral emotional stories. These campaigns use real images and emotionally resonant language to appear credible and inspire immediate donations. Donations made to unverified charities may go directly to individuals with no connection to the cause being promoted. Confirming the registration and track record of any charity through official regulatory databases before contributing is the most reliable protective measure.
Misspelled Brand Names

Brand names in scam communications are frequently misspelled by a single character or written with subtle variations to avoid detection by spam filters. These near-identical names are used in email addresses website domains and even app titles to create the appearance of legitimacy. Familiarity with how a trusted brand presents itself across all official channels makes these inconsistencies easier to detect. Conducting a direct web search for the official brand website rather than following provided links eliminates this risk entirely.
Unscheduled Surveys

Survey invitations offering rewards in exchange for personal or financial information frequently originate from fraudulent sources. Legitimate market research firms obtain participants through established panels and do not distribute high-value rewards for brief questionnaires. The survey format is used to collect answers that individually seem harmless but together constitute a comprehensive personal profile. Being cautious about the quantity and nature of information shared in any unsolicited survey is a reasonable protective approach.
Suspicious Attachments

Email or message attachments from unknown senders or unexpected sources can contain malware designed to compromise your device upon opening. Even file types that appear benign such as documents or spreadsheets can be embedded with harmful code. Verifying the legitimacy of any communication before opening its attachments significantly reduces the risk of infection. Keeping operating systems and security software up to date provides an additional layer of protection against known threats.
Emotional Blackmail

Messages that make you feel guilty responsible or fearful in order to coerce a quick response are employing psychological manipulation rather than presenting a legitimate request. This tactic is used across multiple scam categories including romance fraud fake charity appeals and impersonation schemes. Emotional responses are powerful and scammers are skilled at engineering situations that provoke them intentionally. Taking time to step back and assess a situation rationally before responding is one of the most effective defences available.
If any of these signs have shown up in your online experience share your story in the comments.





